Credential Providers
Developers and security teams love how easy it is to eliminate hard-coded credentials within a broad range of applications using out-of-the-box integrations.

Credential Providers
Let applications securely access the secrets they need
Manage, rotate and secure secrets used by commercial (COTS) applications, RPA, Java, .Net, automation scripts and other non-human identities.
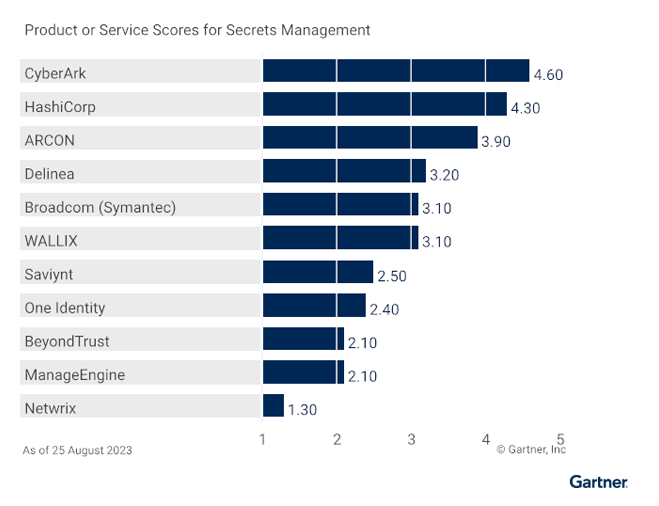
The highest score for Secrets Management use case in the 2023 Gartner® Critical Capabilities for PAM
Explore why CyberArk was ranked highest for the Secrets Management use case.

“The extensibility of CyberArk Secrets Manager has been a huge benefit to us. The out-of-the-box integrations with third party software has simplified how we securely integrate these applications with the rest of our portfolio, which is fantastic.”
Information Security Manager, Top U.S. Hospital
Securely retrieve credentials at run-time
Prevent exposure of hard-coded credentials in static, mission critical applications.
Secure credential access
Passwords that are stored in the CyberArk Digital Vault can be retrieved to the Credential Provider, and then accessed by authorized remote applications.
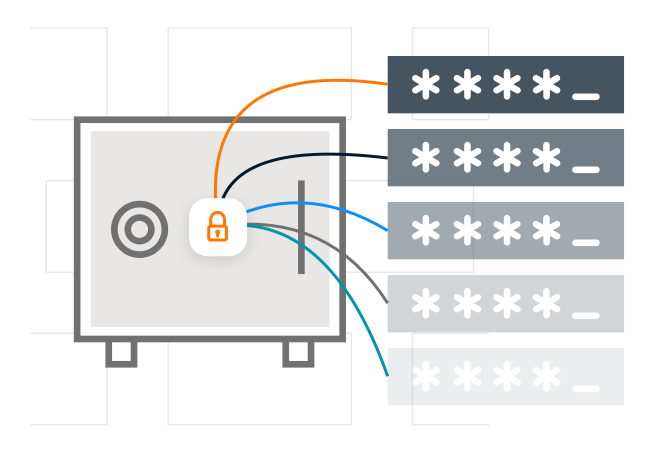
Controlled access
Least privilege enables each application to receive the specific password that it requested and no other.

Strong authentication
Leverages the application workloads native characteristics to strongly authenticate applications and eliminate “secret zero”.

High reliability
Locally cached credentials ensure high availability, business continuity and the highest performance for the enterprise’s mission critical applications.

Fully audited
Audit logs track access to passwords, providing complete monitoring and accountability for each password requested by every application.

Identity security that knows you but doesn’t slow you
Explore all the ways CyberArk gives you peace of mind to move fearlessly forward.
Explore
related
resources
Focus on running your business,
not reacting to threats lorem
Request a demo
Prevent mission critical applications from exposing hard-coded credentials
Simplify securing applications with the broadest range of out-of-the-box integrations
Stay one step ahead of audits and compliance